
Confirm application authenticity
with Code Signing Certificate
Buy or renew a certificate

The benefits of Certum Code Signing Certificate

Application Authentication
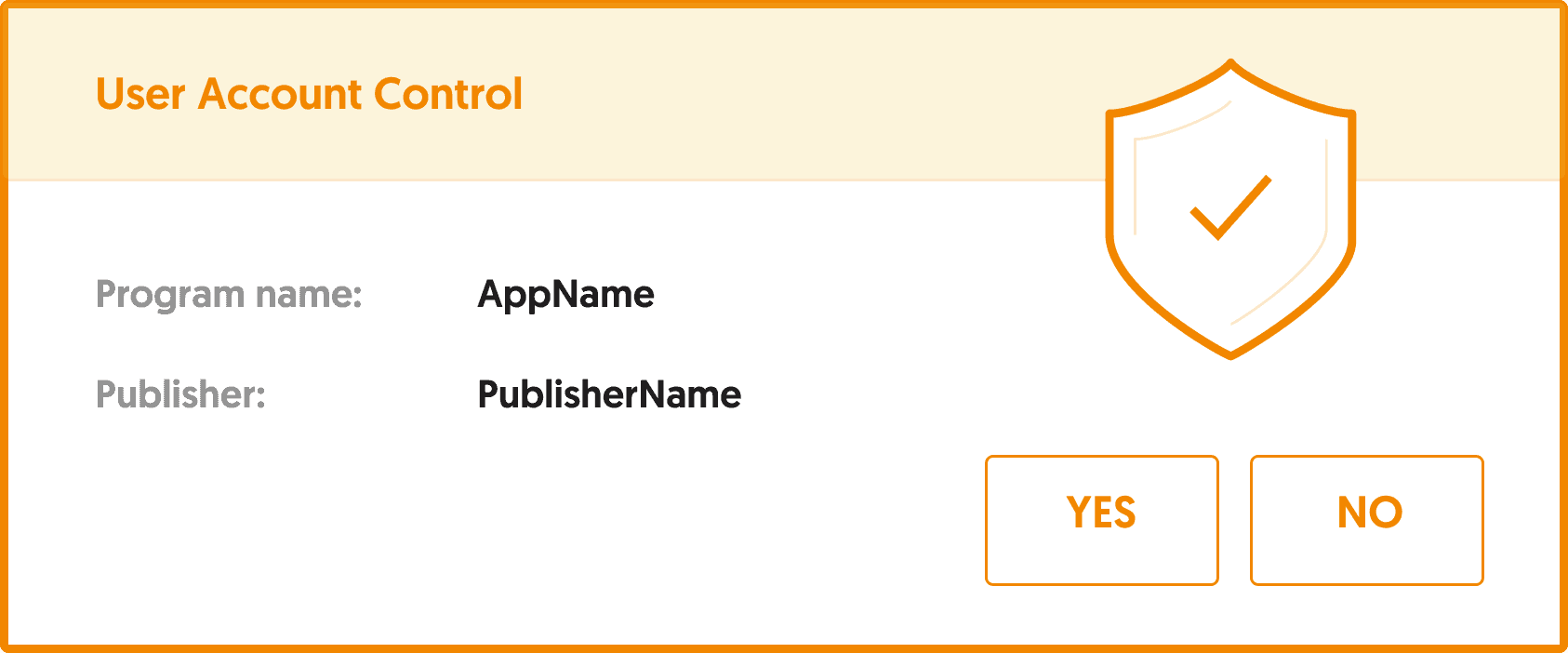
Code Signing Certificate allows you to electronically sign applications, drivers, and programs, therefore ensuring their authenticity and safety.
Thanks to that, the users of your application will gain the confidence that it was not modified, infected, or damaged by any third party.
User Protection

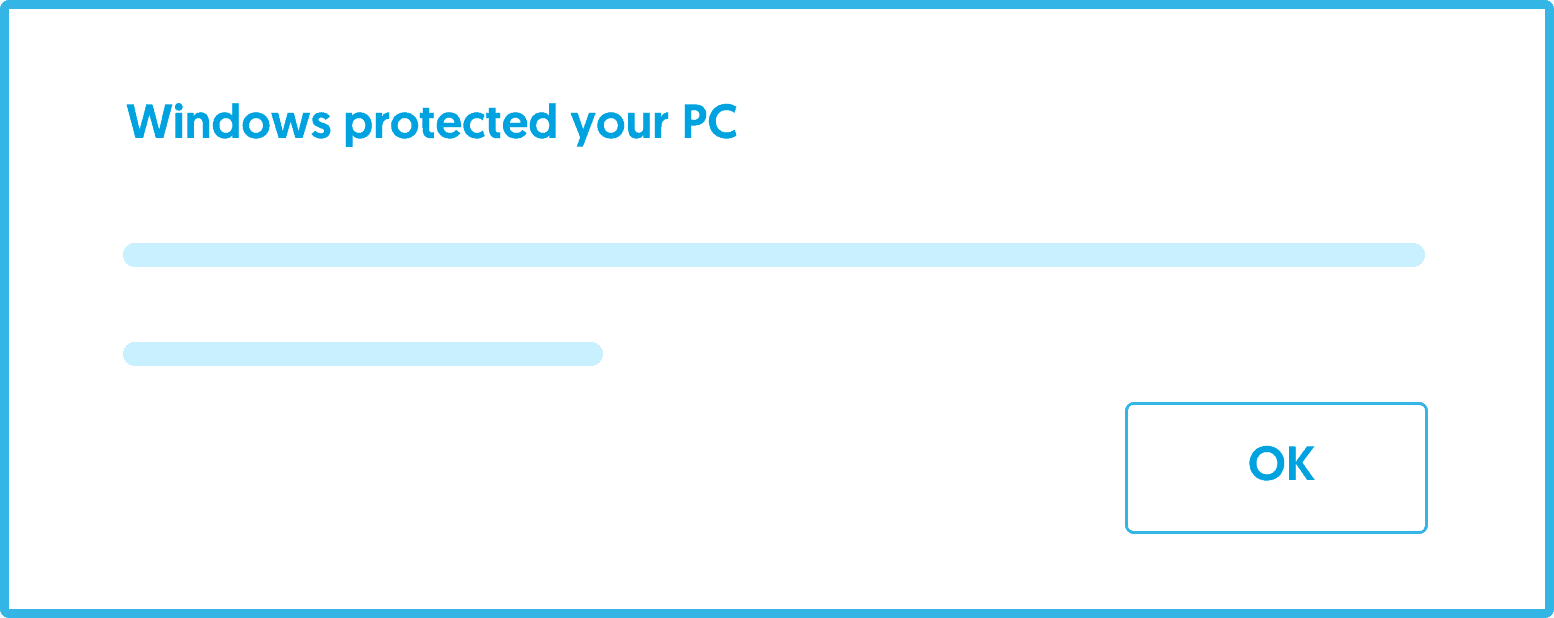
Authenticating your application with Code Signing eliminates the problem of code anonymity on the Web. Thanks to the digital signature, you can be sure that your users will not see the popup about unrecognized applications prevented from prevented from installing or starting. They will trust in the safety of your application.


Brand Reputation

Application certification allows you to protect both the users and your brand’s reputation.
Digital code signing makes using the application completely safe, which impacts your brand’s trust and widens your customer range.
Choose an intelligent solution on a virtual card


The Certificate is uploaded to a cryptographic or virtual card which allows you to sign your code and entire applications, by using well known tools such as signtool.exe or jarsigner.
A virtual card eliminates the need to have a physical token, while still being compliant with safety norms and CA/B Forum rules.


Code Signing
Certificate Family
Opensource
STANDARD
EV
Validity period
1 year
1-3 years
1-3 years
Standard issue time
1-3 days
1-3 days
1-7 days
Data in the certificate
Open Source Developer
First and Last Name/Company Name
Company Name
Financial Warranty
60 000 €
60 000 €
Signing in Kernel Mode
Deleting Microsoft SmartScreen Filter® warnings The certificate eliminates warnings such as “unrecognized publisher” or “dangerous software””